How to Secure Your Dating App Profiles

Securing your dating app profiles requires a combination of strong authentication practices, strategic information sharing, and skepticism toward anyone...

Securing your dating app profiles requires a combination of strong authentication practices, strategic information sharing, and skepticism toward anyone...

The clearest signs that your investment accounts have been hacked include trades you never authorized appearing in your account history, changes to your...
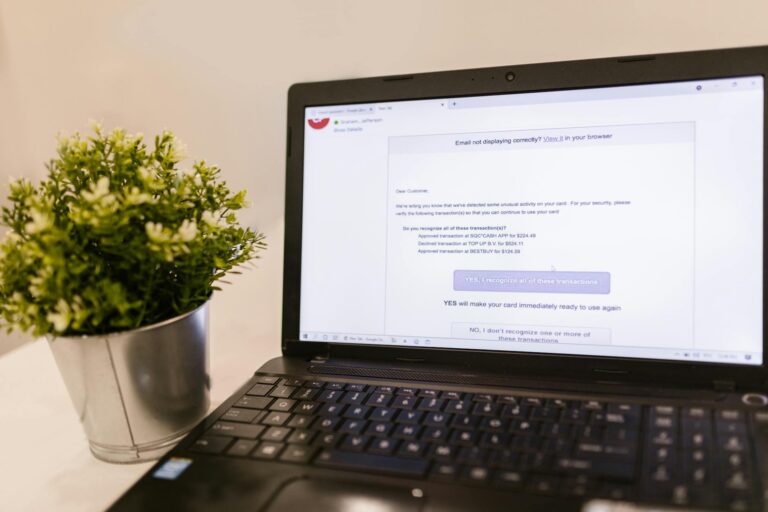
Protecting your work email from phishing requires a combination of technical defenses and personal vigilance.

The fastest way to check if your username was exposed in a data breach is to use a breach notification service like Have I Been Pwned, which allows you to...

Protecting your cryptocurrency from hackers requires moving your assets off centralized exchanges into self-custody wallets, using hardware devices for...

When your passport information is leaked, criminals gain access to one of the most powerful identity documents in existence, enabling them to open...

Securing your cloud storage accounts requires a layered approach: enable multi-factor authentication, use strong unique passwords, audit third-party app...

Securing your cloud storage accounts requires a layered approach: enable multi-factor authentication on every account, use unique and complex passwords...

The clearest signs that your online shopping accounts have been compromised include unfamiliar orders appearing in your purchase history, password reset...

Securing your smart home devices requires a layered approach: start by changing default passwords on every device, segment your IoT devices onto a...