Best Privacy Settings for Google Accounts

The best privacy settings for a Google account start with one toggle: Web & App Activity. Turning it off at Google Account > Data & Privacy > Web & App...

The best privacy settings for a Google account start with one toggle: Web & App Activity. Turning it off at Google Account > Data & Privacy > Web & App...

To protect your call history privacy, start by locking down your phone account with a PIN or passcode, disabling call log syncing to cloud services you...

Telecom breaches expose an unusually broad and sensitive category of personal data, ranging from call and text metadata to Social Security numbers,...

Securing your voicemail starts with one step most people skip: changing the default PIN. Carriers like AT&T, Verizon, and T-Mobile ship voicemail boxes...

The most immediate signs that your cellular account has been compromised include unexpected loss of service on your phone, text messages and calls you...

To protect your mobile number from theft, you need to lock down the three main attack vectors: your carrier account, your SIM card, and the personal...
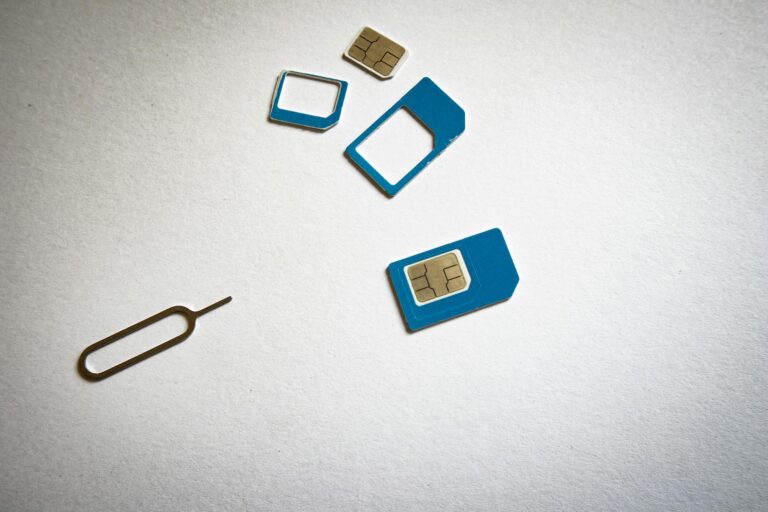
If your SIM card has been swapped, you need to act within minutes, not hours. Call your mobile carrier immediately from a different phone, tell them your...
To check if your phone was cloned, start by looking for the most reliable indicators: unexpected spikes in your cellular bill, text messages or calls in...

The best encrypted email services right now are Proton Mail, Tuta, and Mailfence, each offering end-to-end encryption that prevents anyone "" including...

Protecting your workers' compensation records starts with understanding who can legally access them, how long they must be retained, and what steps you...