What to Do If Your Union Membership Data Is Breached
Understanding what to do if your union membership data is breached is essential for anyone interested in cybersecurity and data breaches.
Understanding what to do if your union membership data is breached is essential for anyone interested in cybersecurity and data breaches.

Lottery scams that leverage stolen personal data share several unmistakable warning signs: they notify you of winnings for contests you never entered,...

The best two-factor authentication apps in 2026 are Cisco Duo Mobile for overall ease of use, Microsoft Authenticator for enterprise integration and...

Protecting your brokerage account online requires a layered security approach: enable multi-factor authentication, use a unique and complex password,...
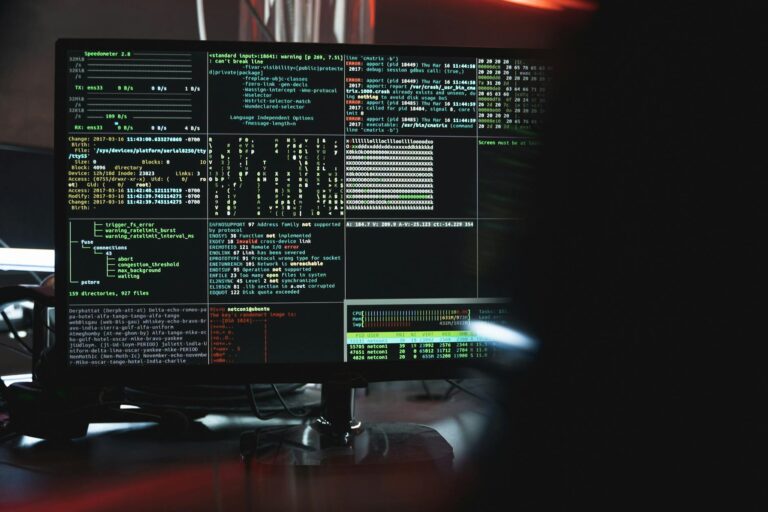
Understanding what information do financial breaches typically expose is essential for anyone interested in cybersecurity and data breaches.

Securing your connected car from hackers requires a layered defense approach: keeping your vehicle's software updated, securing your key fob from relay...

The most telling signs that your Home Assistant device has been compromised include unexpected device behavior such as lights or thermostats activating on...
Protecting your facial recognition data requires a combination of proactive opt-out requests, careful management of your online image presence, and...

If your fingerprint data has been compromised, you need to immediately enable additional authentication factors on all accounts using biometric login,...

Checking whether your biometric data has been leaked requires a fundamentally different approach than monitoring for password breaches.