When dating site data is leaked, victims face a cascade of consequences that extend far beyond a simple password reset. The exposed information””which often includes real names, physical addresses, photos, sexual preferences, private messages, and financial details””becomes fuel for identity theft, extortion schemes, targeted harassment, and in the most tragic cases documented by Toronto Police, suicide. The January 2026 ShinyHunters breach of Match Group, which reportedly compromised over 10 million records from Hinge, Match.com, and OkCupid, demonstrates that even the largest platforms with substantial resources remain vulnerable to attackers seeking this uniquely sensitive data. Unlike breaches affecting retail or social media accounts, dating site leaks expose information people never intended to share publicly.
The Tea dating app breach in July 2025 illustrates this perfectly: 1.1 million private messages were exposed, including deeply personal discussions about abortion planning and infidelity. Victims weren’t just inconvenienced””they were mocked and threatened on social media when their private conversations became public. Two class action lawsuits have since been filed. This article examines the full spectrum of what happens after a dating site breach, from the immediate risks of identity theft and extortion to the longer-term psychological harm and legal fallout that follows. We’ll look at documented consequences from recent breaches, explain why dating apps remain particularly insecure, and outline what users can do to protect themselves in an industry where 75% of apps fail basic security assessments.
Table of Contents
- What Types of Data Get Exposed in Dating Site Breaches?
- How Criminals Exploit Leaked Dating Information
- The Psychological Toll of Dating Data Exposure
- Legal Consequences for Dating Companies
- Government and Military Personnel Face Elevated Risks
- Why Dating Apps Remain Insecure
- Protecting Yourself Before and After a Breach
- The Future of Dating Platform Security
- Conclusion
What Types of Data Get Exposed in Dating Site Breaches?
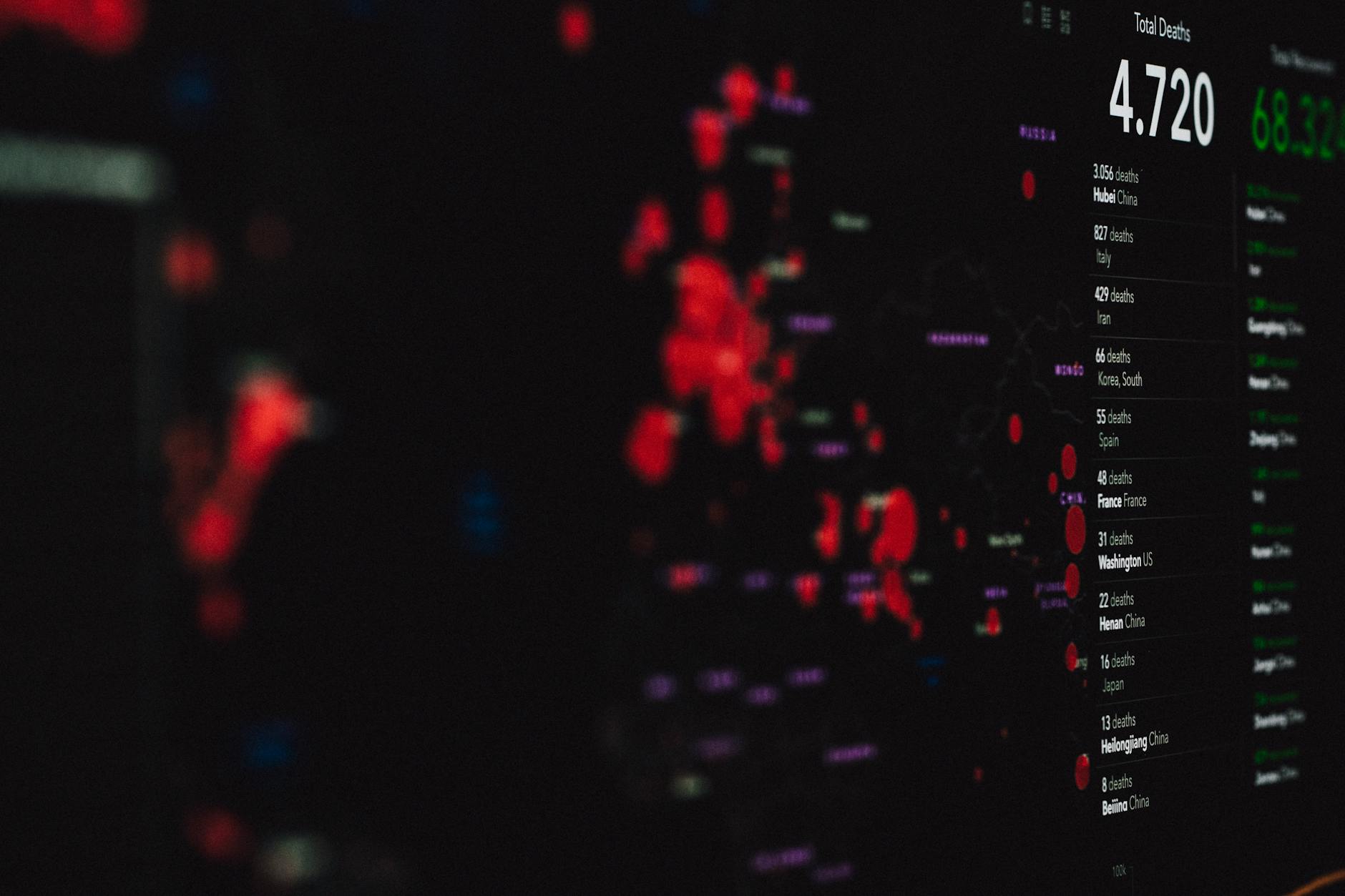
Dating platforms collect an unusually comprehensive profile of their users, which makes breaches particularly damaging. The ShinyHunters attack on Match Group reportedly yielded user IDs, subscription information, transaction IDs, payment amounts, IP addresses, and location data””enough to build a detailed picture of someone’s dating habits, financial situation, and physical movements. The WhiteDate breach in December 2025 went even further, exposing physical appearance details, income brackets, education levels, and IQ-related information for over 6,000 users. The most damaging leaks include visual content. When Senior Dating and Ladies.com left Firebase databases unprotected in October 2024, 917,000 user records were exposed including personal photos and geographic locations.
The Tea breach was worse: 72,000 images leaked, including 13,000 photo IDs and 59,000 selfies that users had submitted for verification purposes. These verification photos are particularly valuable to criminals because they’re typically high-quality images of faces next to government identification. Private communications represent the third category of sensitive data. Dating apps encourage users to share things they wouldn’t discuss elsewhere””relationship histories, health conditions, sexual preferences, and sometimes explicit content. When the Tea app’s 1.1 million messages leaked, conversations spanning from 2023 to 2025 suddenly became searchable by anyone who obtained the data. Unlike a leaked password, you cannot change the content of messages you sent years ago.

How Criminals Exploit Leaked Dating Information
The financial exploitation of dating breach data follows several well-documented patterns. Complete personally identifiable information””full name, address, date of birth””enables traditional identity theft, allowing criminals to open credit accounts or file fraudulent tax returns in victims’ names. More targeted attacks use the leaked data for phishing campaigns: if criminals know which dating service you used, your subscription tier, and your payment history, they can craft convincing fake security alerts that trick victims into revealing banking credentials. Romance scams represent the most lucrative application of leaked dating data. The FBI reported that romance scam losses in the U.S. reached $672 million in 2024, and breach data makes these scams more effective.
Criminals can use leaked profile information to identify promising targets, understand their preferences, and craft personas designed to appeal to specific victims. However, if the breach data is widely distributed rather than held by a single criminal group, victims may receive multiple scam attempts that alert them something is wrong. Extortion is perhaps the most direct monetization method. After the 2015 Ashley Madison breach, extortionists demanded over $200 in Bitcoin from individual victims, threatening to expose their presence on the infidelity site to spouses, employers, or communities. This playbook has been replicated countless times since. Users of niche dating sites””whether focused on extramarital affairs, specific sexual preferences, or particular communities””face elevated extortion risk because the mere fact of their membership may be something they wish to keep private.
The Psychological Toll of Dating Data Exposure
The human cost of dating breaches cannot be measured in dollars alone. Toronto Police confirmed at least two suicides linked to the 2015 Ashley Madison breach, and a pastor whose name appeared in the leaked data also took his own life. These deaths represent the extreme end of a spectrum of psychological harm that includes anxiety, depression, relationship destruction, and social ostracism. When the Tea breach exposed private messages, social media users actively sought out and harassed women whose data appeared in the leak. The shame associated with dating site membership””particularly on platforms serving specific niches””amplifies the psychological impact. Victims often cannot seek support from friends or family because doing so would require admitting they used the service in the first place.
This isolation compounds the stress of monitoring for identity theft, changing passwords across dozens of accounts, and wondering when or if the other shoe will drop. For users of LGBTQ+ dating apps in hostile environments, exposure can mean job loss, family rejection, or physical danger. However, victims’ experiences vary significantly based on the nature of the platform and the content exposed. Someone whose data leaked from a mainstream app like Hinge may face identity theft risk but limited social consequences. A user whose explicit messages or photos leaked from a niche platform faces a fundamentally different situation. The psychological research on data breach victims remains limited, but available evidence suggests that breaches involving sexual or romantic content produce trauma symptoms more severe than those from financial data breaches.
Legal Consequences for Dating Companies
Dating platforms face substantial legal and regulatory consequences when breaches occur. Avid Life Media, the parent company of Ashley Madison, confronted a $578 million lawsuit following the 2015 breach, and CEO Noel Biderman resigned as the company’s reputation collapsed. The Tea dating app now faces multiple class action lawsuits after its 2025 breaches. These suits typically allege negligence in data protection, failure to notify users promptly, and violations of state privacy laws. Financial penalties extend beyond breach-related litigation. Bumble Inc.
paid £32 million in 2024 to settle allegations that it collected biometric data””the facial recognition information used for profile verification””without obtaining proper consent. This settlement illustrates how dating apps face regulatory scrutiny on multiple fronts: not just for security failures, but for the aggressive data collection practices that make breaches so damaging in the first place. The legal landscape varies significantly by jurisdiction. European users benefit from GDPR protections that require breach notification within 72 hours and can impose fines up to 4% of global revenue. U.S. users face a patchwork of state laws, with California’s CCPA providing the strongest protections. If you’re evaluating which dating platform to use, the company’s legal jurisdiction and privacy policy matter””but these documents are difficult to parse, and even compliant companies get breached.
Government and Military Personnel Face Elevated Risks
The Ashley Madison breach revealed several thousand U.S. .mil and .gov email addresses among the user base, raising immediate concerns about blackmail potential against government employees and military personnel with security clearances. Intelligence agencies and foreign adversaries actively seek compromising information about individuals with access to classified materials, and dating site data represents an ideal vector for coercion. Military and government employees face additional complications beyond blackmail risk.
Security clearance applications require disclosure of activities that could create vulnerability to coercion, and failure to disclose can be grounds for clearance revocation. Personnel whose names appeared in dating site leaks faced difficult choices: self-report and risk career consequences, or stay silent and risk worse consequences if the information surfaced later. Some agencies offered amnesty periods to encourage disclosure. For employees in sensitive positions, the guidance is straightforward if unpleasant: assume that anything you do on a dating platform could eventually become public, and make decisions accordingly. This is not paranoia””it reflects the documented reality that dating platforms remain poorly secured and represent high-value targets.
Why Dating Apps Remain Insecure
A 2025 study found that 75% of dating apps are unsafe, and security assessments of Match Group’s portfolio””including Tinder, OkCupid, Plenty of Fish, and Match.com””found that all scored C or below. No dating app achieved an A rating. This industry-wide failure reflects several factors: rapid growth prioritized over security investment, the difficulty of securing user-generated content, and the absence of regulatory requirements specific to dating platforms. The competitive landscape doesn’t help. Dating apps compete primarily on user experience, matching algorithms, and the size of their user bases.
Security remains invisible to most users until a breach occurs, which means companies face limited market pressure to invest in protection. Match Group, which dominates the industry with dozens of brands, faces the same security challenges as smaller competitors but at massive scale””the ShinyHunters breach reportedly included 30 GB of compressed files from Bumble alone. The industry also suffers from the sensitive nature of its data. Security researchers who discover vulnerabilities face legal and ethical complications when reporting them, because demonstrating the flaw often requires accessing real user data. Bug bounty programs exist but tend to be less generous than those offered by financial services or major tech companies. Until dating app security becomes a competitive differentiator or a regulatory requirement, the industry has limited incentive to improve.
Protecting Yourself Before and After a Breach
Users cannot eliminate breach risk while using dating platforms, but they can limit exposure. Use a dedicated email address that doesn’t include your real name. Avoid linking social media accounts. Consider using a Google Voice number rather than your real phone number. Be selective about which photos you upload””anything submitted for verification may end up in a breach. Most importantly, write messages as if they could someday become public, because breach data from 2023 was still being exposed in 2025 Tea leaks. After a breach, move quickly.
Change passwords on the affected service and any accounts where you reused credentials. Enable credit monitoring and consider a credit freeze if the breach included enough PII for identity theft. Search for your email address in breach notification databases to understand what was exposed. If the breach included financial data, monitor accounts closely and consider replacing credit cards. The tradeoff users face is stark: dating apps provide genuine value in helping people form relationships, but using them requires accepting meaningful privacy risk. Deleting accounts after meeting someone reduces ongoing exposure, but historical data may persist in backups or breach datasets. Some privacy-conscious users avoid mainstream platforms entirely in favor of smaller services or in-person social activities, accepting reduced convenience in exchange for reduced risk.
The Future of Dating Platform Security
Regulatory pressure may eventually force industry improvement. The EU’s Digital Services Act imposes new obligations on large platforms, and state-level privacy laws in the U.S. continue to expand. Class action settlements and FTC enforcement actions create financial incentives for better security practices. However, regulation typically lags behind technology, and dating apps continue to collect more data””including biometric information for verification””faster than rules can be written to protect it.
Technical solutions exist but see limited adoption. End-to-end encryption for messages would prevent platforms from accessing user conversations, meaning breaches would expose metadata but not content. Minimal data retention policies would limit what attackers can steal. Decentralized architectures could eliminate the honeypot of centralized user databases. These approaches involve real tradeoffs for platforms””reduced ability to moderate content, enforce policies, and monetize data””which explains their limited adoption despite clear security benefits.
Conclusion
Dating site breaches produce consequences that ripple outward from the initial exposure. Victims face immediate risks of identity theft and extortion, followed by longer-term psychological harm and the permanent loss of privacy over intimate communications. Companies face lawsuits, regulatory penalties, and reputational damage.
The human toll””documented suicides, destroyed relationships, harassment campaigns””represents a category of harm that financial settlements cannot repair. The industry’s failure to prioritize security, with 75% of apps rated unsafe and no platform achieving an A rating, means users must treat breach risk as inevitable rather than hypothetical. Limiting the data you share, using dedicated contact information, and communicating with awareness that your messages could become public represent the current state of self-protection. Until market pressure or regulation forces meaningful change, the question is not whether dating platforms will be breached, but when and how badly.
