What to Do If Your Utility Account Is Compromised
If your utility account has been compromised, you need to act immediately: contact your utility provider to report the unauthorized access, change your...
If your utility account has been compromised, you need to act immediately: contact your utility provider to report the unauthorized access, change your...

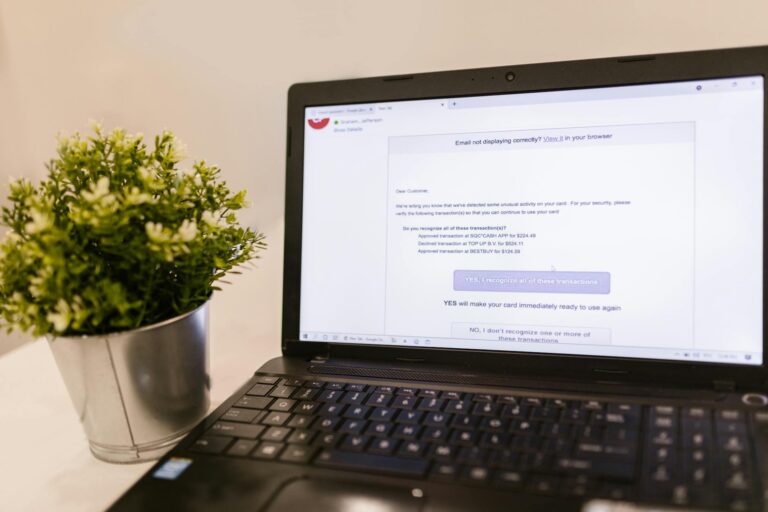
Fake tech support scams reveal themselves through a predictable set of warning signs: unsolicited contact claiming your computer is infected, urgent...
The best dark web monitoring services for most individuals and small businesses are those that combine automated credential scanning with actionable...

Protecting your student loan information starts with treating your loan account credentials with the same vigilance you would apply to your bank accounts.

Data brokers collect an extensive range of personal information about you, including your full name, home address, phone numbers, email addresses, date of...

Securing your dating app profiles requires a combination of strong authentication practices, strategic information sharing, and skepticism toward anyone...

The clearest signs that your investment accounts have been hacked include trades you never authorized appearing in your account history, changes to your...
Protecting your work email from phishing requires a combination of technical defenses and personal vigilance.

If you've received a hospital data breach notification, you need to act immediately: place fraud alerts on your credit files, review the breach notice...

The fastest way to check if your username was exposed in a data breach is to use a breach notification service like Have I Been Pwned, which allows you to...